The Host Unknown Podcast
Episode 49 - Have Your Bunnies at the Ready
Episode Summary
We are recording a day earlier than usual so next week's Smashing Security podcast may feature more outdated stories than usual.
Episode Notes
April 1st!
https://www.facebook.com/burgerking/posts/4438200159526619
https://twitter.com/VW/status/1376868756782219266
https://www.animationmagazine.net/tv/the-cats-out-of-the-bag-cn-rebrands-as-cat-toon-network/
This week in Infosec
Liberated from the “today in infosec” twitter account:
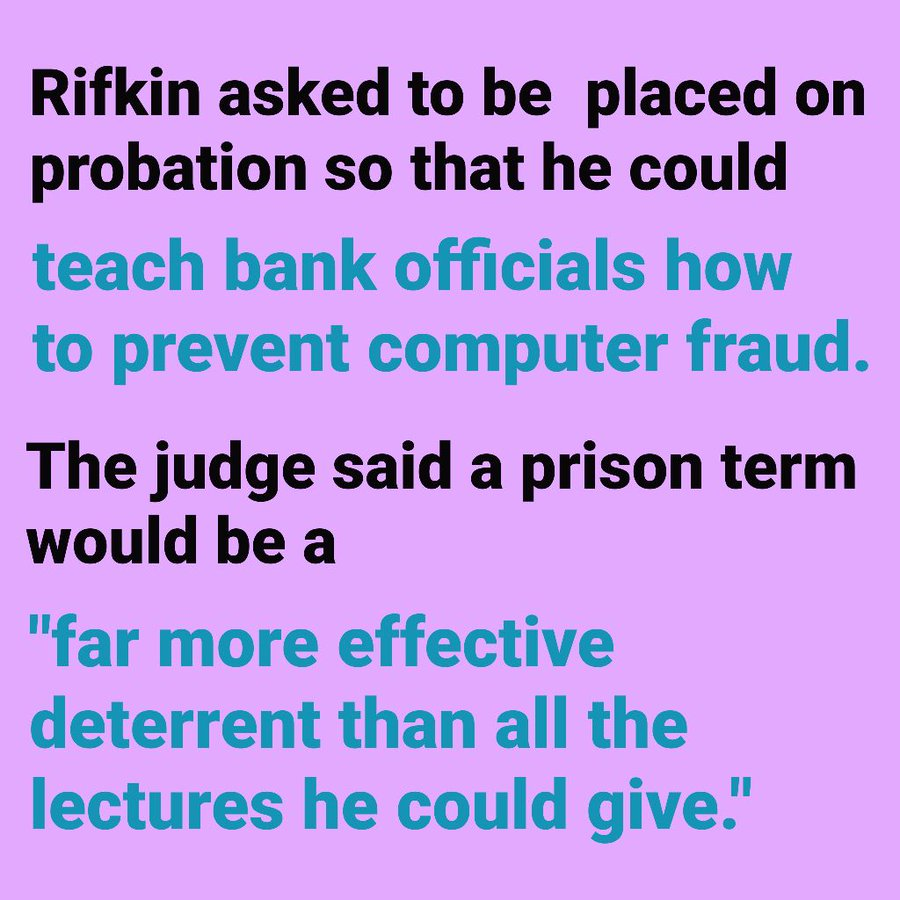
- 27th March 1979: 33-year-old computer consultant Stanley Mark Rifkin was sentenced to 8 years in prison for stealing $10.2 million from a bank via computer. Federal District Judge Matthew‐Byrne Jr., rejecting an appeal from Mr. Rifkin that he be placed on probation.
https://twitter.com/todayininfosec/status/1243427187165814785
https://www.social-engineer.org/wiki/archives/Hackers/hackers-Mark-Rifkin-Social-Engineer-furtherInfo.htm
Rant of the Week
Whistleblower: Ubiquiti Breach "Catastrophic"
https://krebsonsecurity.com/2021/03/whistleblower-ubiquiti-breach-catastrophic/
https://community.ui.com/questions/Update-to-January-2021-Account-Notification/3813e6f4-b023-4d62-9e10-1035dc51ad2e
Billy Big Balls
Thoughts on Selling to Security Leaders
Jason Chan - VP Security Netflix
- If I ask to not be contacted by your company, ensure that fulfilling my request covers all channels (phone, LinkedIn, email, snail mail, etc.) and extends to your colleagues.
- Don’t sell based on FUD (Fear, Uncertainty, and Doubt). Security is a tough field to work in, and bad things happen. I don’t need scare tactics from sales folks.
- It’s fine to follow up to an unanswered message - once. And give it at least a week between messages. If someone doesn’t respond after the second reachout, it’s likely they are not interested. I’d not have time to do my job if I replied or unsubscribed to every reach out I receive.
- Don’t assume you understand the problems I’m facing or that you know what should be at the top of my priority list. Every organization has a different threat model, culture, and risk tolerance.
- If you’re selling something, don’t ask to “pick my brain” or for “feedback on your approach.”
- DO NOT CALL ME ON THE PHONE. There is no situation where I'm looking to have this conversation. Email or LinkedIn is fine.
- If you’re working with someone on my team, don’t escalate to me if things don’t go your way. I trust my team to make good decisions.
- Your solution or product doesn’t solve every security problem. That’s okay, I don’t expect it to. Just be clear about the value you believe your solution brings.
- Your solution won’t save me from the next [INSERT BREACH/EXPLOIT/VULNERABILITY] here. Don’t say it will. Perhaps it’s additive or helpful, but operating a security program successfully is complex and involves people and technology working together. Again, just be clear about your product’s value.
- Don’t offer me a gift card, gift, or cash in exchange for a meeting. Just no.
- Keep your word, and follow up on time if and when asked. I appreciate folks who meet their commitments and respect my time.
- If I’m a customer, think long term partnership vs. transactional sale. There is a lot of overhead to switching vendors and I appreciate folks that I can build a long term, mutually beneficial relationship with.
Industry News
FBI Issues Mamba Alert
Burned Out Employees Put Corporate Security at Risk
Aussie TV Network Taken Off Air by Ransomware
German MPs Hit by Russian-Backed Phishing Attacks
Cyberbullying Linked to Social Media Addiction
UK Cyber Security Council Officially Launches as Independent Body
CISA and RH-ISAC to Run Cybersecurity Drill
Three-Quarters of Legal Breaches Caused by Insiders
Most Global Chip Companies Show Signs of Compromise
Tweet of the Week
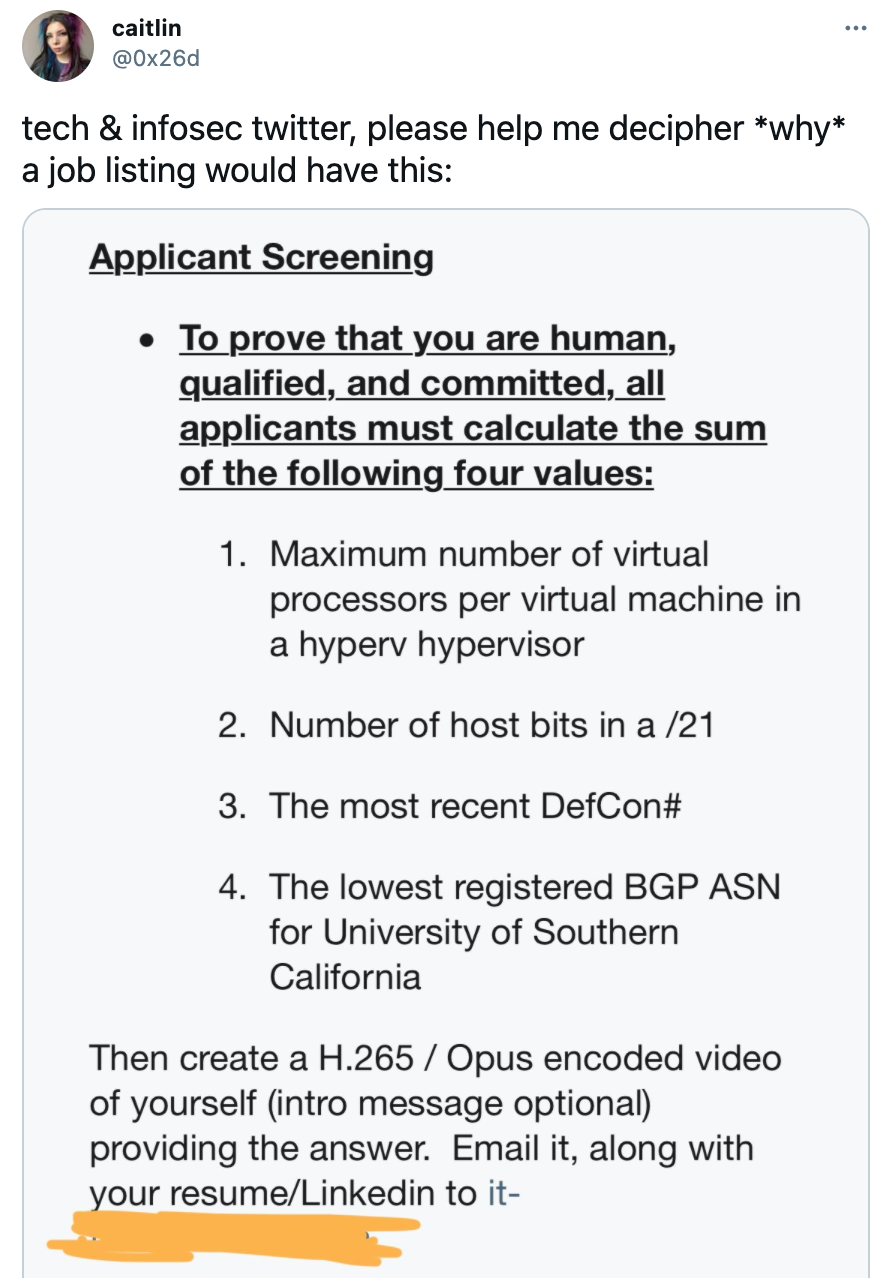
https://twitter.com/0x26d/status/1377415060759269377